The Ever-Expanding Universe of Data
From enterprise applications to the internet of things (IoT), the number of connected devices which produce data is growing at a staggering rate. Business Insider forecasts that by 2020 more than 24 billion internet-connected devices will be installed around the globe [1]. It’s no wonder analysts from IDC predict that by 2025 the world will produce 175 zettabytes of data, a tenfold increase from what was generated in 2016 [2].The vast majority of this data is forecast to be unstructured. While much of this unstructured data will reside within Object Storage based services, a large amount, and likely the most actively accessed, will reside in network attached storage (NAS) leveraging the SMB and NFS protocols within datacenters.
Traditional systems with their inherent limits on managing unstructured data at scale will be unable to handle the coming data explosion. And new requirements around auditing and compliance will leave business vulnerable to fines as administrators struggle to manage complex environments with legacy tools. In these times of higher scrutiny, easy to use and integrated tools need to operate at web scale to help protect and monitor file data.
Challenges with Data Auditing and Compliance
Nutanix developed Nutanix Files to eliminate the complexity of siloed NAS deployments. But storing data comes with additional challenges outside of core NAS functionality, including data insights, auditing, and compliance.Every industry faces different challenges when it comes to their compliance objectives. Personal information which falls under GDPR, credit card payments impacted by PCI-DSS, or health records falling under HIPAA all have unique standards which could apply. Even within a given industry, requirements may differ. For example, in the U.S. each state has different laws which mandate medical record retention requirements, varying anywhere from 2 to 30 years [3]. These are commonly based on the date of the medical record such as age since the last patient contact or discharge, or maintaining records until a patient reaches a certain age. These requirements also depend on entity, typically linked to either medical doctors or hospitals.
Some common auditing goals for NAS deployments include:
- Storing the audit details of all user activity
- Detection of malicious activity including operations from viruses or ransomware. Also improper end user operations including the bulk copy of data
- Unintended user action including the accidental deletion of data
- Permission minimization, ensuring the right users at the right time have appropriate access to the right data. This includes knowing which users can access specific files, or what files certain users can access.
- Data classification, which can be age based or dependent on data type linked to regulatory requirements.
- Data retention and tiering, where classifications are used to move data to different storage targets, including to the public cloud based on these same age and regulatory requirements.
Introducing Nutanix File Analytics
Nutanix Files offers a rich auditing API to which applications can subscribe and receive real-time notifications of file related events. These events include file creation, deletion, read operations, write operations and permissions changes among other activities. A common use of these APIs is forwarding these events to a syslog server for retention and audit trails. While logging audit trails is useful functionality simplifying insights into this data is a must.Nutanix File Analytics was developed to consume this native auditing API while delivering additional insights to the underlying data and user activity.
Activity Logging
File Analytics captures all file activity for registered file server instances. This logging helps to form an audit trail so administrators can review what operations have occurred against specific data and by specific users.Intelligent Insights
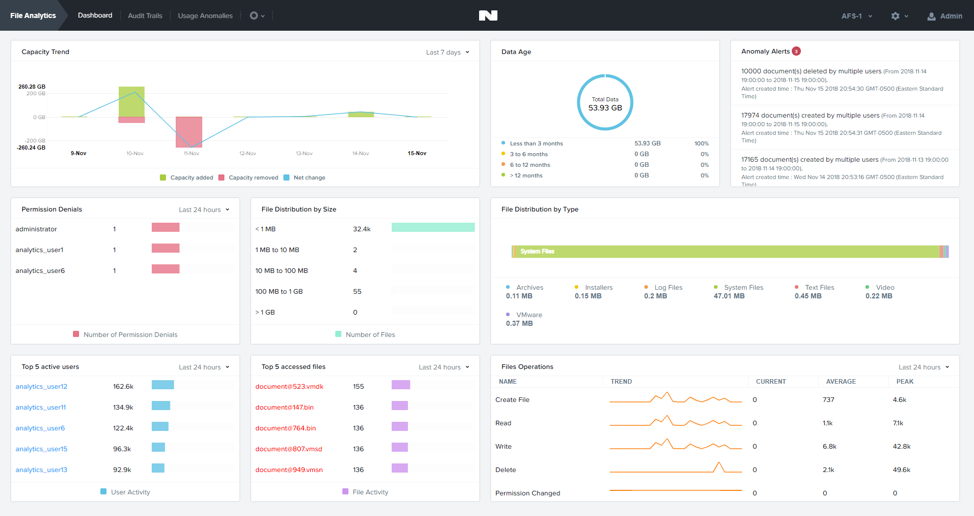
Logged events are analyzed to provide an initial dashboard of information which shows:- Capacity trend: what’s being consumed and how it’s changed over time.
- Data age: which calculates the last time a file was accessed and shows the percent of data at varying age ranges.
- Anomaly alerts: All file operations which exceed a given anomaly threshold, like the deletion of a large number of files, are shown in this area of the dashboard.
- Permission Denials: the number of permission denial events for specific users over the selected time range.
- File distribution by size, which shows the number of files within a given size range.
- File distribution by type, details the amount of storage consumption represented by file type categories, such as log files, image files, video files, etc.
- The top 5 active users based on total operations over the selected time period
- The top 5 accessed files based on total operations over the selected time period
- File Operations: details the most frequent types of operations, like file create, read, write, etc over a selected time period, including the trend over that time
The dashboard provides a quick and easy health check so you better understand capacity trends, data age and file activity that could indicate malicious activity.
Audit Trails
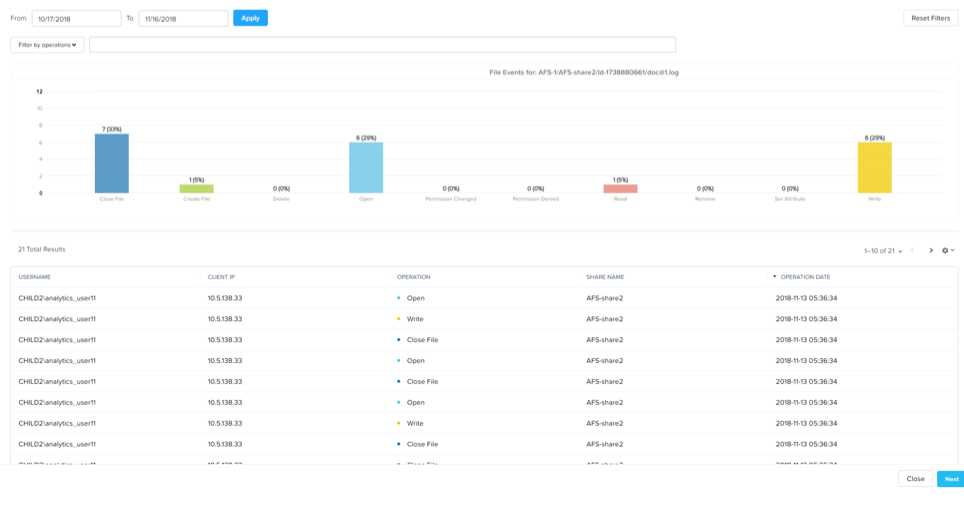
Audit trails allow you to search for a specific file or a specific end user to find all file or user activity for a given timeframe. You can search for a given file or user based on wildcards. The frequency and types of operations, by users and against files, including the time they occurred are displayed over your specified time period. You can further filter the audit trail based on operation type, such as open, read, write, delete and other events.Being able to search user and file activity helps you monitor access activity against sensitive data. These insights can help you with any data access minimization requirements.
Real time Monitoring
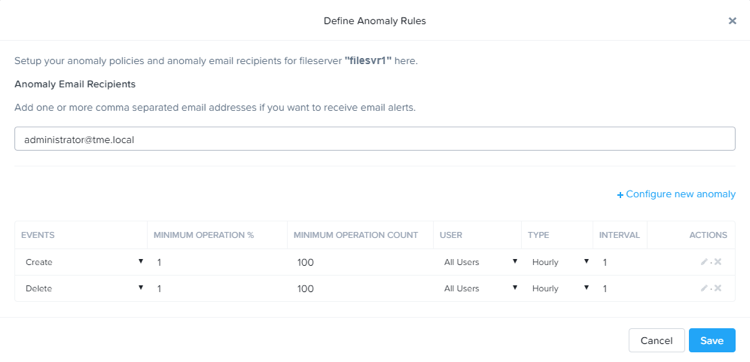
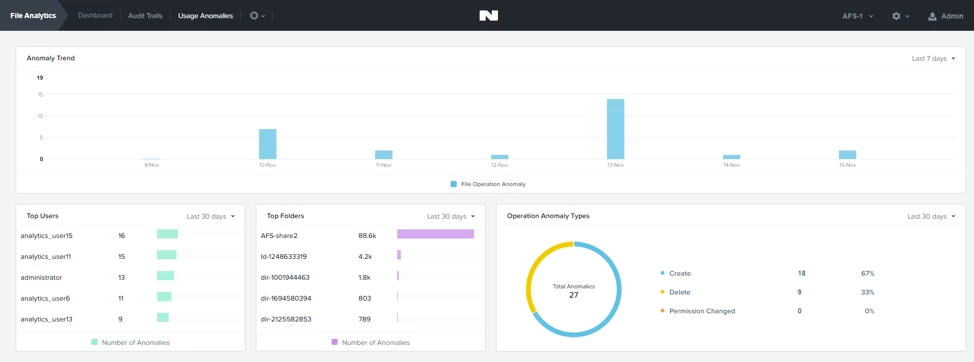
File analytics allows you to define anomaly alerts which represent specific operations as executed by an individual or against the file server as a whole.You can specify different events, such as permission changes, file deletes, file creates, etc. and define an operation percentage and operation count as a part of the alert. You also specify the interval for the operations in question for when these thresholds apply. You can optionally specify email recipients for the anomaly events.
As anomaly events occur, the email addresses defined in the anomaly rule will received detailed information. You can also monitor each anomaly alert and track them over time via the usage anomalies dashboard. The dashboard shows you the users which caused the anomaly and the folders that were impacted. The types of anomalies and trends are also detailed.
Strange access patterns which trigger anomalies can indicate malicious user, virus or ransomware activity. Seeing this activity and being alerted in real time can help you stop these operations and better understand user access patterns across your organizations.
Future Plans
The first release of File Analytics is available as a technical preview in the Nutanix Files 3.5 release. The features touched on in this blog only represent the first step to where we are heading with Analytics. Future plans include automatic anomaly alert creation based on machine learning. Access pattern bands can be derived automatically from existing data. Activity outside of these bands will indicate an anomaly that requires attention.Organizations also strive for data retention and tiering solutions across data age and compliance classifications. The data age collected by File Analytics will help to tie in a future tiering framework to move data to S3 compatible targets. As data hits a certain age, tiering definitions can move data to other storage locations, including the public cloud. Also, classifying data with user defined tags, such as compliance requirements, will be a future addition with Nutanix Files to aid in tiering and retention decisions.
A Fully Integrated Solution
File Analytics is fully integrated into the Nutanix management experience. Initial deployment is integrated right into Prism. You simply download the Analytics bundle and perform a one-click deployment. Once deployed you can launch the File Analytics page where you enable analytics against the desired file server instances running on your cluster.Just like Nutanix Files, File Analytics provides a simple, modern and scalable solution. File Analytics helps you better understand how data is utilized by your organizations to help you meet your data auditing, data access minimization and compliance requirements.
Forward Looking Statements Disclaimer
This blog post includes forward-looking statements concerning our plans and expectations relating to new product features and technology that are under development, the capabilities of such product features and technology and our plans to release product features and technology in future releases. These forward-looking statements are not historical facts, and instead are based on our current expectations, estimates, opinions and beliefs. The accuracy of such forward-looking statements depends upon future events, and involves risks, uncertainties and other factors beyond our control that may cause these statements to be inaccurate and cause our actual results, performance or achievements to differ materially and adversely from those anticipated or implied by such statements, including, among others: the introduction, or acceleration of adoption of, competing solutions, including public cloud infrastructure; a shift in industry or competitive dynamics or customer demand; and other risks detailed in our quarterly report on Form 10-Q for the fiscal quarter ended January 31, 2019, filed with the Securities and Exchange Commission. These forward-looking statements speak only as of the date of this press release and, except as required by law, we assume no obligation to update forward-looking statements to reflect actual results or subsequent events or circumstances.© 2019 Nutanix, Inc. All rights reserved. Nutanix, the Nutanix logo and the other Nutanix products and features mentioned herein are registered trademarks or trademarks of Nutanix, Inc. in the United States and other countries. All other brand names mentioned herein are for identification purposes only and may be the trademarks of their respective holder(s).
Footnotes
[1] https://www.businessinsider.com/there-will-be-34-billion-iot-devices-installed-on-earth-by-2020-2016-5
[2] https://www.seagate.com/files/www-content/our-story/trends/files/Seagate-WP-DataAge2025-March-2017.pdf
[3] https://www.healthit.gov/sites/default/files/appa7-1.pdf